What to Do If Your Computer Is Hacked

In a world where there is a cyber attack every 39 seconds, it’s paramount to know what to do if your computer is hacked. Cybercriminals are getting craftier by the day, and you need to know what actions to take if the worst comes to worst.
Well, we’re going to show you exactly how to do just that. Plus, we’ll also discuss how to know if your computer is hacked, so that you don’t make any rash decisions.
How to Know If Your Computer Is Hacked – 12 Signs
1. You Can’t Access Your OS
True, one of the main reasons you might not be able to log into your operating systems is hardware failure or OS-related issues. But we’re not talking about that. In that case, your computer will generally keep restarting, or you’ll be booted into your OS’ Safe Mode instead.
What we’re referring to is getting a message that outright tells you your OS is locked down, and you won’t be able to access your files. You’ll be told to send a certain amount of money (a few hundred $ or more) to a cryptocurrency wallet address (usually a Bitcoin one), or a PayPal address. The message will state that if you don’t send the money in a certain amount of time, all your data will be wiped.
Sometimes, you might even be able to log into your OS, and see your computer’s desktop. But you won’t be able to do anything on it other than interact with the files left by the hacker, and see the new desktop background photo, which would normally be the message mentioned above.
If you’re in that situation, there’s no doubt that your computer has been hacked. Specifically, it was infected with ransomware – a type of malware that holds your data hostage until you pay up. To find out what you should do in such a scenario, skip to the “What to Do If your Computer Is Hacked With Ransomware” section below.
2. You See a Fake Antivirus/Antimalware Message
While this tactic is no longer as widely used by hackers as it was before, it’s still a sure sign that your computer has been compromised. In fact, the moment you see such a notification on your computer, it’s already too late since the infection has already spread to your OS.
Why do hackers bother with these notifications, then? Well, these fake messages are just the cybercriminal’s attempt at installing even more malware on your device. Alternatively, they might try to trick you into paying money for their “solution.” If you do that, not only will you waste money, but you’ll also have your credit card details stolen.
How do you know the antivirus/antimalware message is fake? Well, the best way to spot the differences is to know what your antivirus/antimalware provider’s notifications and messages normally look like. However, here are some signs that might give the fake message away:
- You get spammed with messages telling you your computer is infected with malware and viruses.
- The message has a spammy tone, and the writing contains grammatical errors.
- The colors of the messages don’t match the brand colors of the legit antivirus/antimalware program you’re using.
- You’re asked to download free software off the web to solve the security issues.
- Closing the message by hitting “X” does nothing, or it redirects you to the online page where you’re supposed to download the free “solution.”
3. You Get Bombarded With Pop-Up Ads and Messages
Much like fake antivirus/antimalware messages, random pop-up messages and ads are also a sure sign your computer has been hacked. A normal one just won’t spam you with stuff like that.
Usually, this is caused by adware – malware that infects your computer with tons of ad-related pop-up notifications and messages. The ads you see can be for anything – drugs, medicine, pornography, video games, music, etc. They’ll often contain short, shady links that take you to phishing websites if you click on them. That can also happen if you hit the “X” button to close the message, though.
Also, if you try to close the messages, they’ll just pop up again in a few seconds. That, or new ads and messages will flood your screen whenever you try to close one.
4. You’re Missing Files/Programs and Notice New Ones
If you suddenly can’t find files or programs you knew you had on your computer, there’s a chance you’re dealing with a malware infection. Hackers tend to use malware that gives them remote access of victims’ computers. They then steal any sensitive information they might find (work files, intimate photos, etc.), delete it from the target’s computer, and try to blackmail them with that data. They might also uninstall or disable security programs.
Of course, remote control of your computer isn’t always the cause. Malware like worms and Trojans are also programmed to delete any files they come across to wreak havoc on your computer.
Besides that, you might also notice new programs on your computer, and new icons on your desktop. Those are called PUP (Potentially Unwanted Programs), and are files/programs installed by hackers which contain malware. If you interact with them, or perform any action that triggers their activation, your computer will be infected with even more malware and viruses.
5. Your Browser Has New, Unwanted Toolbars
It’s not hard to spot unwanted toolbars since they tend to clog your browser to the point where they might take up a quarter of the screen or more. Plus, they usually have a spammy design and weird names that make them stand out from normal toolbars – not to mention they try to redirect you to shady websites.
“At least I can easily get rid of them, right?”
Yeah, it’s usually enough to remove them, and reinstall your browser. However, the problem is that if your browser has been tampered with, it’s extremely likely your computer has been exposed to malware infections too.
6. Your Online Searches Get Redirected
If you type in anything in your browser or search engine, and you get redirected to a completely different website, it’s usually a dead giveaway that your computer was hacked. For example, googling “dog food” redirects you to a website about email marketing and lead generation.

This usually happens because a cybercriminal is using malware and security exploits to control where your browser is directing your connection requests. Most of the time, they do this because they are paid to deliver clicks to someone’s website, or because they want to drive a lot of traffic to an ad-infested website to make quick ad revenue.
However, sometimes, a hacker could redirect your browser search queries to a malicious phishing website. In that case, not only will your device be exposed to even more malware, but you’ll also have sensitive information stolen (like your credit card details, email login credentials, or bank account information).
7. Your CPU/GPU Is Being Used at Full Capacity
Having your CPU or GPU “put to work” (so to speak) while playing one of the latest video games is pretty normal, but they shouldn’t be used at full capacity, making very loud noises, and overheating.
If you notice that happening every time you start your computer, there’s a very big chance that it was infected with cryptomining malware. Basically, a hacker is using your computer’s graphics card and/or processor to mine for cryptocurrencies. Not only will that drive up your electricity bill, it can also make your computer slower, and damage your GPU, CPU, and fans through overheating.
You should also become alert if you just notice that your computer case fans are noisier than usual. That can happen if too much dust accumulates, but if you clean your computer, and the noise persists, there’s a chance cryptomining malware is at play. It’s just that the cybercriminal crontrolling it is trying to keep it a secret, so he/she is not using your computer’s full power.
8. Your Contacts Receive Spammy Messages/Emails from You
If your friends, family, or work contacts are asking you about weird messages they received from your email address and/or social media profiles, it’s safe to say you’ve been hacked. The messages might contain shorten, shady links, pornographic content, or might outright ask your contacts to share sensitive information, which will be swiftly stolen.
Basically, either a cybercriminal has managed to take over your accounts, or they released malware in your computer that automatically replicates by sending out malicious messages to your contacts.

Sometimes, the hacker or malware might create tons of spammy posts on your social media profiles that contain malicious links. Anyone that interacts with them will have their own computer infected with the same malware.
9. Your Passwords Are No Longer Working
If you try to log into your email address, social media profile, bank account, or operating system, and get a message telling you the login credentials you entered are wrong, there’s a chance you’re the victim of a cyber attack.
Sure, you might have just entered the wrong password or username, or missed a character or two. That can happen.
However, if you are 100% you’re typing in the correct credentials, the only explanation is that a cybercriminal has managed to take over your accounts, and has locked you out of them. They can manage such a feat by using malware, phishing messages, or exploiting security vulnerabilities to steal sensitive data from you, like usernames and passwords.
10. Your Computer Does Things on Its Own
Is your mouse cursor moving by itself, preventing you from running security scans or interacting with icons on your desktop? That’s likely because a hacker has remote access to your computer, and can control it from the comfort of their own home. Cybercriminals normally manage to do that by infecting computers with Trojans and rootkits.
The biggest mistake you can make in this case is thinking that those “involuntary” actions taken on your computer are just glitches or hardware bugs. If you ignore them, the hacker will likely wait until your computer idles (when you’re not using it, basically), and use it to empty your bank accounts, and steal personal data which can later be sold on the deep web. They might also try to spread the malware to other people in your contacts list – either through email or social media messages.
11. Your Online Accounts Are Missing Money
We’re not just talking about missing $10-$20, though you should definitely contact your payment provider or bank if you notice regular unapproved transactions, no matter how small the amount is.
The classic sign that your computer has been hacked is an empty (or nearly empty) bank account. If a cybercriminal goes through all the effort to hack your device, they’re going to take as much money as they can. So, if you suddenly see you’re missing hundreds or thousands of $, you now know what the main cause could be.
Basically, a hacker might have infected your computer with malware that allows them to monitor your activities – including your keystrokes. Then, they just use that info to break into your accounts, and steal your money.
12. Your Antivirus/Antimalware Program No Longer Works
If your security software has suddenly stopped working, or you just noticed it was disabled, that can be a sign of a cybercriminal having control over your computer. That’s especially true if you can’t start up the antivirus/antimalware program at all, or if it has been uninstalled without your permission.
True, a system restore point could cause that too, but if you’re also not able to start your operating system’s Task Manager or Registry Editor, then there’s no doubt you’ve been hacked.
What to Do If Your Computer Is Hacked – Follow These 8 Tips
Before we get started, we should mention that these tips will only help if you have a second computer or laptop you can use. Of course, it should have no traces of malware infections or hacking activities.
If you don’t have a second device you can use, see if you can use one of your friends’ computers. Just make sure they run an antivirus/antimalware scan beforehand.
1. Isolate Your Computer
First things first, you need to make sure your computer is completely isolated from the Internet. So, make sure you remove all Ethernet cables, and turn off WiFi connectivity. If your device has a switch to turn off WiFi, use that instead of the software switch since a hacker can tamper with that to turn it back on. If you’re worried that your router might have been hacked too, you can disconnect it as well.
Since some malware or viruses can harm your computer even when it’s not connected to the web, we recommend disconnecting the device from the power source too.
2. Remove and “Clean” the Hard Drive
Next, take out the hard drives from your computer, and connect them to the second computer or laptop. Ideally, the device should run a powerful security program, like Malwarebytes and ESET.
We recommend using a USB drive caddy to connect the compromised hard drives to the second device since it’s safer. If you really need to place them in the computer or laptop, make sure they are set to secondary “slave” drivers. Otherwise, they’ll boot up first, and infect the second device with your malicious operating system.
Once you have safely connected the hard drives in the second computer or laptop, run a scan with the antimalware/antivirus program installed on it. Quarantine and delete any infections that are found.
When the hard drives are clean, back up any data you need from them – stuff like work files, personal photos and videos, important documents, etc.
Afterwards, completely wipe your hard drives. It might sound unnecessary after you just ran a security scan and got rid of all malware, but it’s better to be safe than sorry. You can do that with services like Disk Wipe or DBAN, but you can also check out the other options on this lengthy list.
3. Reinstall Your Operating System and Security Software
After you’re done cleaning the hard drives, it’s time to put them back into your main computer. Once everything is set up, reinstall your operating system.
Once your OS is up and running, install the necessary drivers (motherboard, GPU, CPU, etc.). However, for the moment, we recommend not installing your LAN/Internet drivers yet. Before you do that, install your antivirus/antimalware program first to make sure you have a line of defense when you connect to the web. If you don’t have an installer, just download it on the second device, and put in on a USB stick.
Also, a bit unrelated but still important to mention – in the future, make sure your antivirus/antimalware software is always up-to-date. If it isn’t, it might not be able to keep up with the latest cyber attacks and malware.
When everything is configured, copy all the data you backed up from your hard drives.
4. Contact Your Bank and Payment Processors
If some of your money has gone missing, you need to get in touch with your bank as soon as possible. Let them know what happened, and that a hacker stole money from you. Depending on the situation, your bank might be able to help you recover the funds.
If you use an online payment platform like PayPal or Payoneer, you should contact their representatives as well if money has gone missing from those accounts.
Even if none of your funds are missing, it might still be a good idea to at least give your bank a heads-up that you’ve been the victim of a cyber attack.
5. Reset All Passwords & Set Up Multi-Factor Authentication
Even if your online accounts haven’t been tampered with, it’s still a good idea to reset all your passwords. Ideally, you should come up with strong passwords, and make sure you use a different one for each account. Also, to boost their security, you should change them on a regular basis.
If you need help coming up with powerful passwords, we wrote an article on that topic.
Beside that, you should enable any form of multi-factor authentication on your accounts. The standard is two-factor authentication, where you need to use a randomly-generated code on your phone to complete the login process. That way, even if a hacker manages to steal your password, he/she won’t be able to access your accounts.
However, if your accounts are already compromised, it’s best to create new ones from scratch. It’s a hassle, but it’s much safer to do that.
6. Let All Your Contacts Know About This
Tell everyone (your family, friends, and even work colleagues) that your computer was hacked so that they know to ignore and report any suspicious messages they might receive from your social media and email accounts.
Make sure you stress how important it is to make sure they don’t click on any shady links they might have gotten from you, or open any attachments that were sent to them.
7. Install a VPN, and Use It When Browsing the Web in the Future
A VPN (Virtual Private Network) is an online service that can hide your IP address and encrypt your web traffic. While it can’t combat malware infections, it can help you secure your traffic while browsing the web.
Basically, if you don’t use a VPN, cybercriminals can exploit WiFi vulnerabilities to monitor your online traffic. By doing that, they can steal valuable information from you – like your login credentials, the contents of your messages, and your credit card or bank account details. With that kind of data, any hacker could easily steal money from you, and hack into your computer.
“But that’s only a risk if I’m using public WiFi, right?’
True, public WiFI is extremely unsafe to use – especially since most networks don’t use any encryption at all. However, your own home network has its flaws too. After all, even if you’re using WPA2, cybercriminals can still crack it with the right cyber attack. And that problem will only be fixed when WPA3 rolls out, but that might be years away.
So, you’re better off just using a VPN on your home computer at all times – alongside a secure antivirus/antimalware program, preferably. If you want to make things simpler, just set up the VPN connection on your router. That way, any time your computer (or any other device) connects to your home network, it will automatically use a VPN connection.
Need a VPN You Can Rely on?
CactusVPN is just the solution you need. Our service can make sure you’re always safe on the web by:
- Encrypting all your data with military-grade encryption.
- Securing your connections with powerful protocols like SoftEther and OpenVPN.
- Safeguarding your online browsing from DNS leaks with built-in protection.
- Ensuring your traffic is never exposed – even if you encounter connection errors – with a high-end Kill Switch.
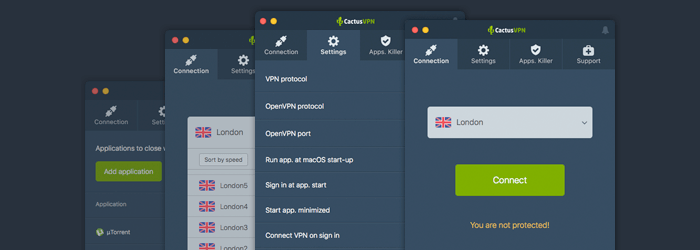
Plus, our service works across multiple platforms, and comes with a free trial. You don’t need to give out any credit card details, and you get access to all our service’s features.
Special Deal! Get CactusVPN for $3.5/mo!
And once you do become a CactusVPN customer, we’ll still have your back with a 30-day money-back guarantee.
What to Do If your Computer Is Hacked With Ransomware
Well, let’s address the first thing that’ll go through your head – should you pay the ransom or not? Most security experts advise against doing that since the cybercriminal could have the ransomware delete or refuse to decrypt your data anyway. On the other hand, you might be lucky, and the hacker might hand over the decryption key. Stuff like that has happened before when a hospital chose to pay a $55,000 ransom.
You can also try contacting law enforcement, though you shouldn’t 100% rely on them. How fast your problem is solved depends on how laws treat ransomware situations in your country, whether or not your police force has a dedicated cybercrime unit, and what other criminal issues take priority over your own. Since you’re dealing with a time limit with ransomware, waiting around isn’t really a good option.
So, if none of the options above are something you want to try, you might be successful with the following steps:
- First, you need to isolate your computer. The moment you notice it’s infected with ransomware, you need to unplug it from the power source, Internet/WiFi network, and any storage devices (like external hard drives).
- See exactly what kind of ransomware you’re dealing with it. Normally, that should be easy since the ransomware message usually names the infection. If it doesn’t you can try using ID Ransomware or Crypto Sheriff to identify it.
- Use The No More Ransom Project to see if you can get rid of the infection, and find a way to recover your files without paying any ransom. You can also try using Kasperky’s decryptors to see if any of them help you.
- If the ransomware only locked your web browser, just open your computer’s Task Manager, and terminate the process for the browser. Restart the system, and run an antimalware scan.
- If you manage to recover some of the files you need, you should completely wipe your hard drives. You can also get newer ones if you prefer that option. Next, you just need to do a clean install of your operating system. Unfortunately, this might be the only thing you can do if you’re unsuccessful in recovering the data that’s taken hostage too.
Usually, the best thing to do is take preventive measures – use powerful antivirus/antimalware software, avoid phishing messages, and always keep an offline backup of the important data on your computer.
The Bottom Line
Well, first, ask yourself this “is my computer hacked?”
To know that for sure, here are some clear signs you should look for:
- Random pop-up messages and ads that keep crowding your desktop.
- Fake antivirus/antimalware messages that claim your system is infected (not far from the truth, to be honest), and that you need to download “free” software by following shady link.
- Your mouse cursor starts moving on its own, and you notice that some of your files have been deleted or moved to different folders.
- New programs and icons start appearing on your desktop.
- There are new toolbars on your browser you never installed.
- All your Internet searches get redirected to shady websites.
- You friends, family, and work colleagues say they’ve been receiving weird, spammy messages from your accounts.
- You can no longer log into your online accounts since the passwords you enter are wrong.
- Your CPU and GPU start heating up excessively when you start your OS, and they make a lot of noise.
- Your antivirus/antimalware program no longer works, or has been uninstalled.
- Money starts disappearing from your online accounts.
- Lastly, you get a message saying you can’t access your OS or files if you don’t pay a ransom to decrypt them.
If any of those signs are familiar, here’s what to do if your computer is hacked:
- Isolate your computer from the web.
- Take out the hard drives, and connect them to a second computer/laptop that’s malware/virus-free. If you need to insert the hard drives in the second device, make sure they’re set to be a secondary “slave” driver.
- Run antivirus/antimalware scans on the hard drives, recover what data you can, and then wipe them.
- Place the hard drives back in your main computer, and reinstall your operating system.
- After installing some necessary drivers, install a reliable antivirus/antimalware program. Do that before installing the web drivers.
- Contact your bank and the online payment platforms you’re using if money has gone missing.
- Let all your contacts know about this. They need to ignore any malicious messages they might have received from you.
- Install a VPN on your computer, and use it to secure your online connections in the future.
Now, if you’re dealing with ransomware, your options include paying the ransom, contacting the authorities, or trying to handle things on your own. Unfortunately, the first two options are not always the best ones, and you’re not guaranteed any results. You might be successful on your own (isolating the computer, identifying the ransomware, using The No More Ransom Project or Kasperky’s decryptors to get rid of the ransomware, recovering some files and wiping the hard drives), but you shouldn’t get your hopes too high since it might sometimes be impossible to recover from a ransomware attack. Your best option is to prevent it.
 What Is Cyberstalking? (9 Ways to Keep Yourself Safe)
What Is Cyberstalking? (9 Ways to Keep Yourself Safe)
 How to Secure Your Smart Home in 7 Steps
How to Secure Your Smart Home in 7 Steps
